You need a proactive and highly qualified cyber team to manage evolving cyber-threats, compliance mandates, and shifts in the way the world does business. LMT is a (System and Organization Controls) SOC 2 Type II compliant company – this certification proves that we are dedicated to protecting client data from unauthorized access, security incidents, and other vulnerabilities.
Our certified cybersecurity experts use layered security strategies, advanced security solutions, advisory services, and security awareness training, to build a cybersecurity program that keeps your company one step ahead of cyber-threats.
HAVE YOU SECURED YOUR BUSINESS?
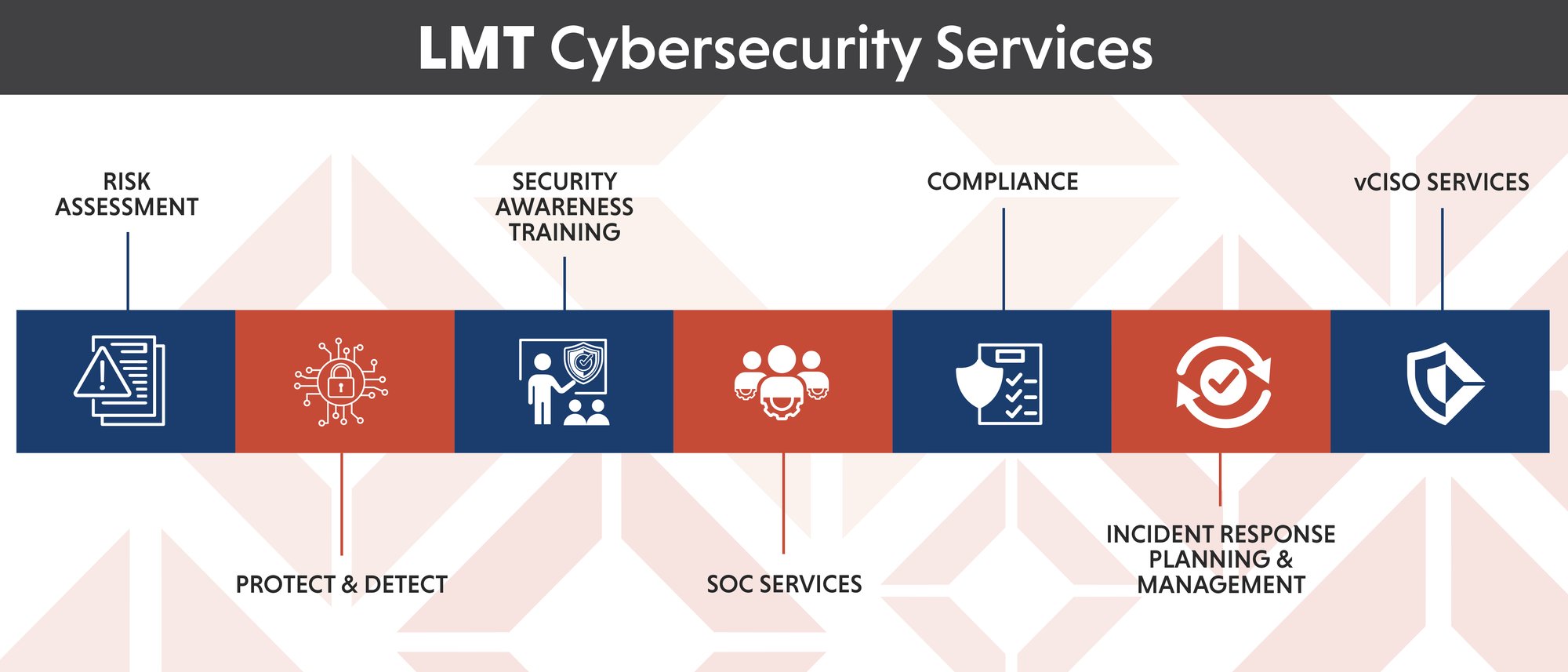
Risk Assessment
“Life is inherently risky. There is only one big risk you should avoid at all costs, and that is the risk of doing nothing.” ~Denis Waitley
Your company is constantly changing with new technologies, vendor partnerships, and shifts in your workforce. These changes affect your IT systems and risk exposure. LMT will take a big-picture snapshot of your current cyber risk exposure, revealing vulnerabilities and uncovering opportunities to improve defenses, secure your data, and protect your reputation.
Protect & Detect
“An ounce of prevention is worth a pound of cure.” ~Benjamin Franklin
Anti-virus software only responds to known threats, leaving opportunities for cyber-criminals to benefit from zero-day vulnerabilities.
We implement a zero-trust framework using Advanced EDR, AI, and Machine Learning tools to detect traces of suspicious behavior and protect your systems from being hacked.
![]()
Security Awareness Training
“Education is not the learning of facts, but the training of the mind to think.” ~Albert Einstein
Your employees are a vital part of your cybersecurity defense strategy. We aim to develop a security mindset for your employees through Security Awareness Training. By arming them with knowledge of how to identify suspicious content and behaviors, this training will transform your employees from being the weakest link to a robust part of your active defense.
SOC Services
“If you don’t invest in risk management, it doesn’t matter what business you’re in, it’s a risky business.” ~Gary Cohn
Effectively protecting your business from today’s frequent, costly threats requires a dedicated resource focused solely on safeguarding your sensitive data and critical business systems. A security operations center, or SOC, is a team of cybersecurity experts that effectively monitors, detects, and responds to threats, giving you peace of mind.
Compliance
“Regulatory compliance is critical to managing risk.” ~Hendrith Vanlon Smith Jr.
Understating and implementing compliance controls and regulations is overwhelming and time-consuming for businesses. LMT can help your company navigate the complexities of industry compliance regulations such as CMMC, NIST CSF, NYDFS HIPAA, PCI, and more. Under the guidance of a CISSP, CMMC-RP, LMT will audit your environment and work with your team to build an expertly designed cybersecurity program to bring your company into compliance.
Incident Response Planning & Management
“The average cost of Information Technology (IT) downtime is $5,600 per minute.”
~Gartner
The first step to managing an incident is to have a well-thought-out plan established before you ever need it. Planning facilitates and expedites the response time in identifying, analyzing, and correcting a data breach. Our experienced cybersecurity professionals work with you to build a plan for remediation, documentation, and incident management should the need arise.
vCISO
“A CISO actually needs to know more than any other individual C-level position in order to protect all aspects that fall under all other C-positions.” ~Andrew Farkas
Rely on a vCISO from LMT to have the technical expertise, business insight, and communication skills to make an immediate difference. Our CISSP certified professionals serve a broad range of industries for companies of various sizes and know how to align strategies with your unique IT environment, needs, and challenges. Our vCISO’s will:
- Provide executive level advisory services on a flexible basis.
- Offer neutral expertise as they set strategic objectives to support business technology demands.
- Spearhead the creation and implementation of a cybersecurity program that evolves with your company.
- Lead, implement, and manage security and compliance standards.
- Evaluate data protection practices, including third-party access to sensitive data.
- Focus on the high-level cybersecurity needs of your company, allowing your IT team to focus on day-to-day responsibilities





